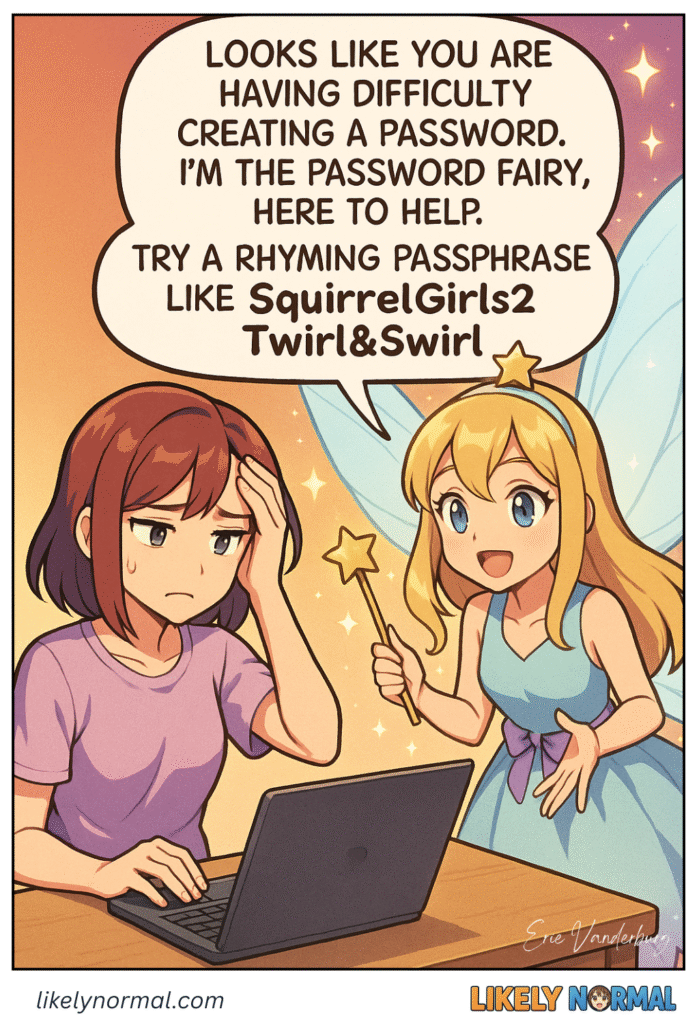
You know that moment of sheer panic when a website rejects your fifth password attempt while simultaneously demanding uppercase letters, hieroglyphics, and the DNA sequence of a rare tropical frog. Just as you’re about to surrender and type “Ch33zeLover77” yet[…]↓ Read the rest of this entry…
Posts Tagged account
The world is in chaos. The streets stand empty, the shelves lie bare, and humanity’s greatest fear is not only death, but running out of Clorox wipes and toilet paper. That’s when our hero (or villain, depending who you ask)[…]↓ Read the rest of this entry…
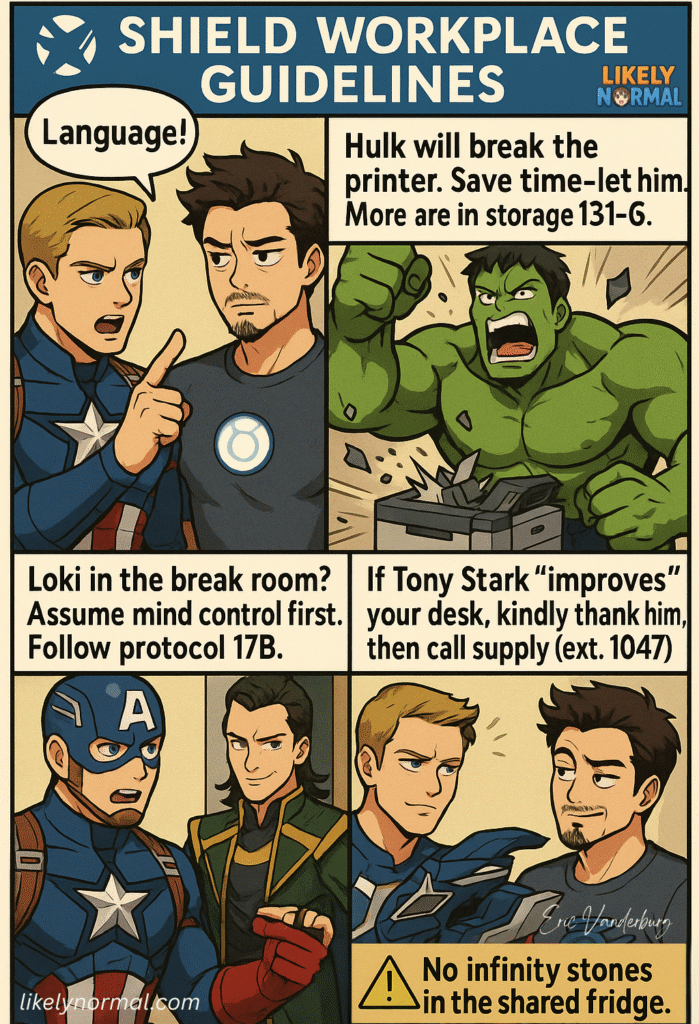
If there’s one thing SHIELD agents excel at (besides dramatic trench coat entrances and surviving improbable explosions), it’s preparing for the absolute worst-case scenario. And by “preparing,” we mean writing ridiculously detailed contingency manuals that account for everything from alien[…]↓ Read the rest of this entry…
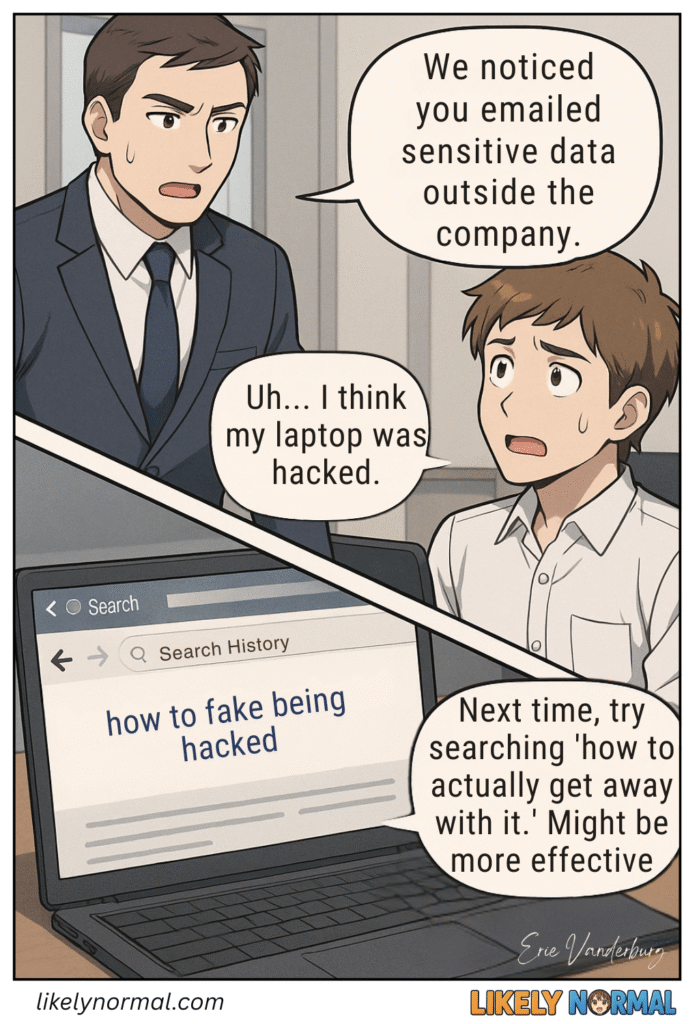
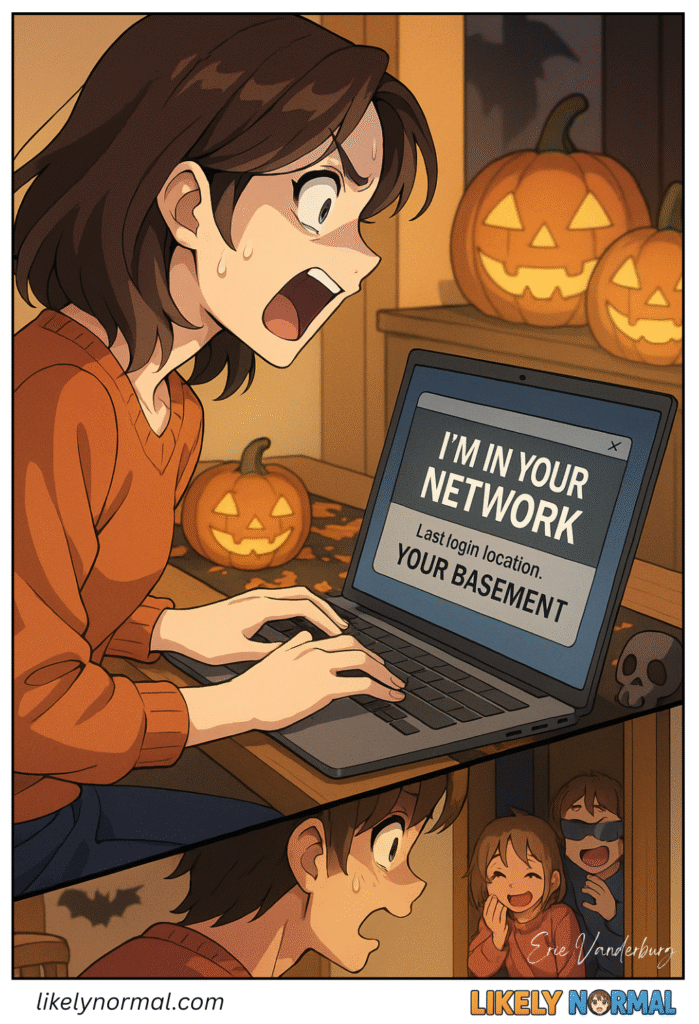
Working in cybersecurity, I’ve heard just about every defense there is, but there is something special about the “I was hacked!” claim. Whether it’s a suspicious Facebook post, an accidental email reply-all disaster, or a mysteriously maxed-out credit card, someone,[…]↓ Read the rest of this entry…
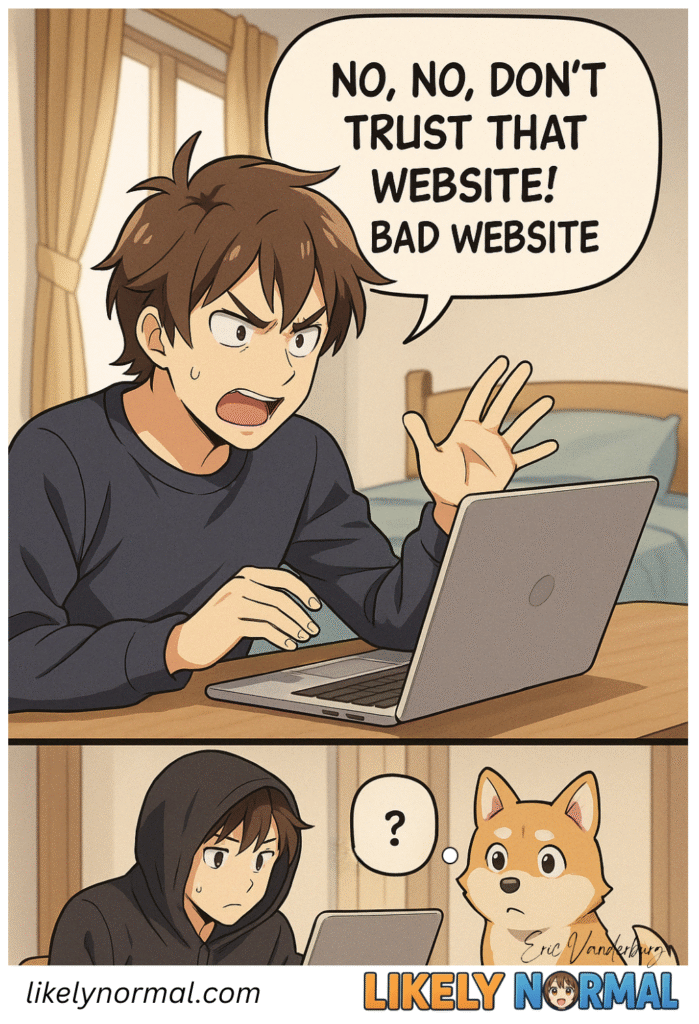
Explaining online safety to someone with low digital literacy often turns us into frustrated dog owners yelling “NO! BAD WEBSITE!” at their screens like they’re scolding a golden retriever chewing on a power cord. The struggle is real: how do[…]↓ Read the rest of this entry…
Once attackers breach your perimeter defenses, they enter a wonderland of security oversights where the real “work” of hacking becomes almost laughably easy. It’s like spending months picking a high-security lock only to find the vault door inside was left[…]↓ Read the rest of this entry…
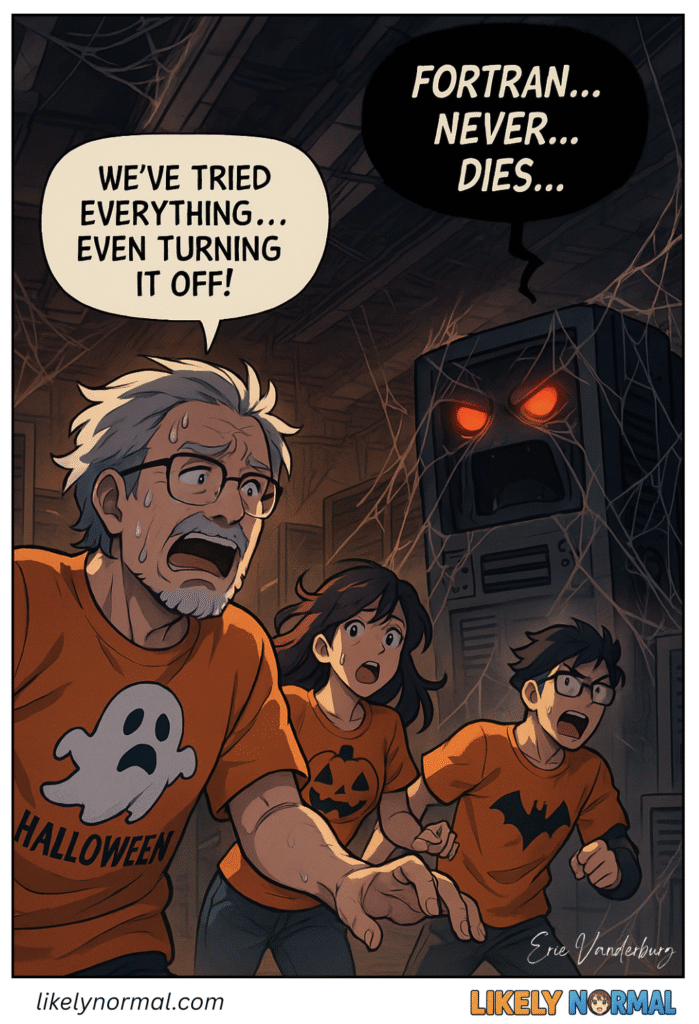
Deep in the bowels of government research labs and financial institution basements, two technological elder gods slumber restlessly – FORTRAN and COBOL, the programming equivalents of mummies that refuse to stay in their tombs. These linguistic relics from the dawn[…]↓ Read the rest of this entry…
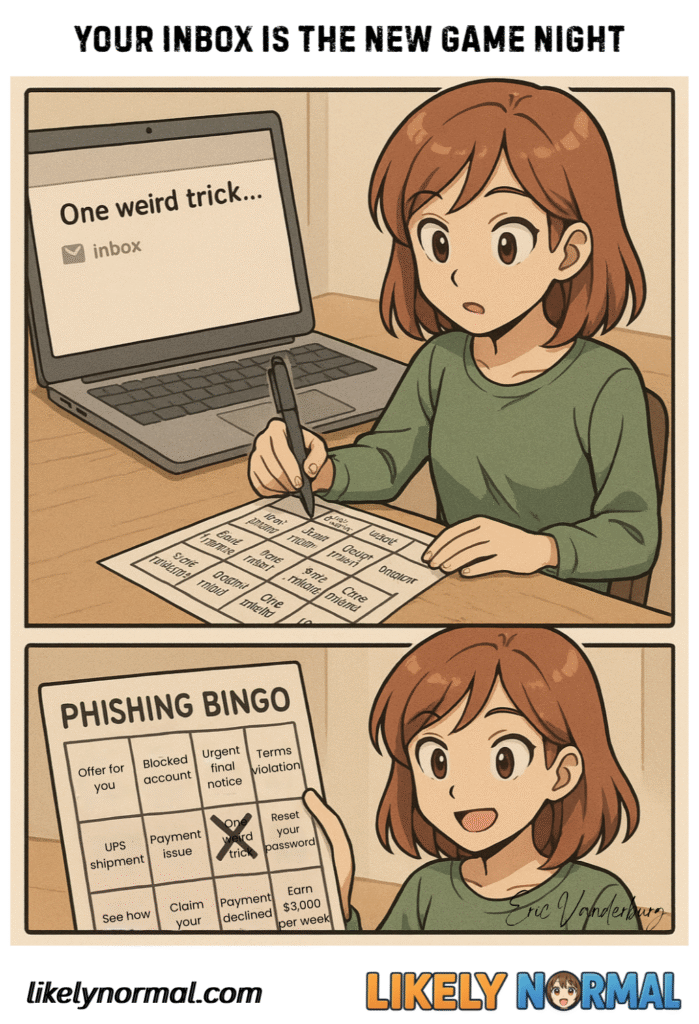
Remember those classic road trip games where kids pass the time by finding certain things out the window? There’s “I Spy,” “License Plate Bingo,” and the always exciting “Who Can Find the Most Cows” competition. Well, here’s the digital age’s[…]↓ Read the rest of this entry…
Alternate Access Methods
We treat digital security like we’re building Fort Knox, complete with firewalls that could withstand a nuclear attack, encryption protocols that would make a cryptographer dizzy, and enough multi-factor authentication steps to qualify as an obstacle course. Yet somehow, hackers[…]↓ Read the rest of this entry…
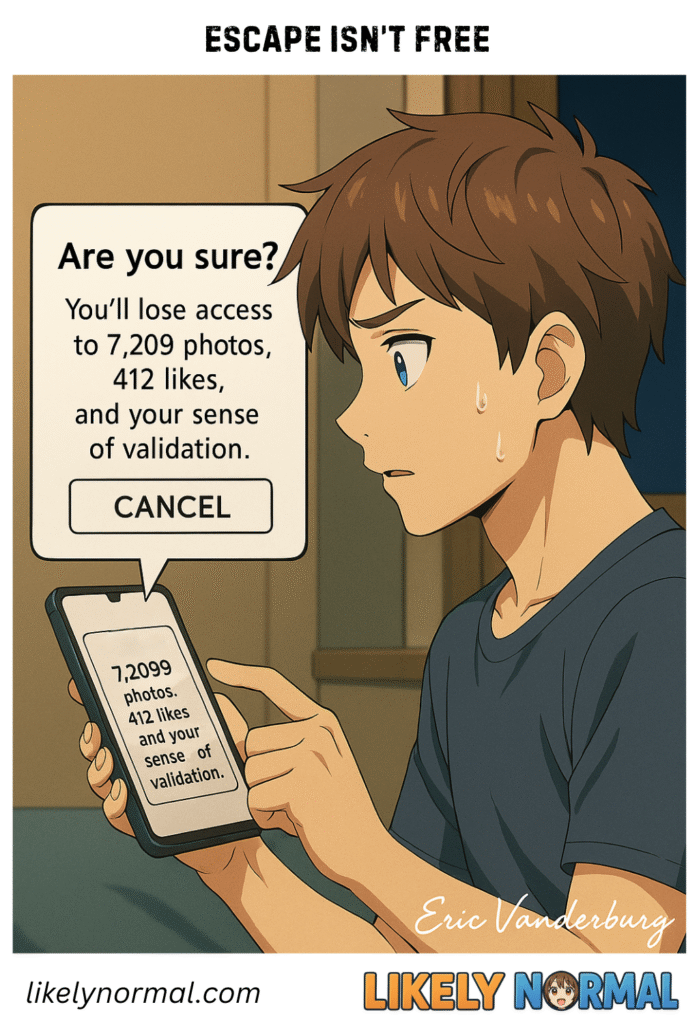
Trying to quit social media is like breaking up with a clingy ex who also happens to be holding your childhood photos hostage. “Oh, you wanna leave? Cool, cool. Say goodbye to… checks notes… your entire identity and sense of[…]↓ Read the rest of this entry…